- 首页
-
菜单
- 家园币
-
比特币
Financial Markets by TradingView
您正在使用一款已经过时的浏览器!部分功能不能正常使用。
- 主题发起人 菲沙河谷
- 发布时间 2015-04-03
更多选项
导出主题(文本)中国翻墙者被劫持为黑客 Github遭史上最大攻击
文/
Sylar
(泡泡报道) IT技术人员的圣地Github正在受到该论坛史上最大的网络攻击,Github日前在其博客上公开说。各方分析显示,此次攻击来自中国,且攻击技术高超:基本上,中国的翻墙者正在无意识中被劫持加入网络攻击,成为肉鸡。Github在博客中表示,此次攻击是“为了迫使其删除一些内容”。据分析认为,此次攻击具体是针对网络自由组织GreatFire等在Github上提供的免翻墙信息服务,但影响到了整个Github。
更新(3月30日北京时间20:00):
3月30日,在中国外交部的例行记者会上,当记者问到最近的网络攻击是否来自中国时,交部发言人华春莹并未“否认”,也为对此作出正面回答,强调“中国是黑客攻击最主要的受害者之一”:
近期似乎只要是美国或者其他哪个国家有网站受到攻击,就会有人联想是不是中方黑客所为,这很奇怪。我想提醒你,中国是网络黑客攻击的最主 要的受害者之一。我们一直强调,中方希望同国际社会一道,加快制订国际规范,共同维护好网络空间的和平、安全、开放与合作。希望各方都能以积极、建设性态 度合作应对网络黑客攻击问题。
翻墙上百度,网民变黑客
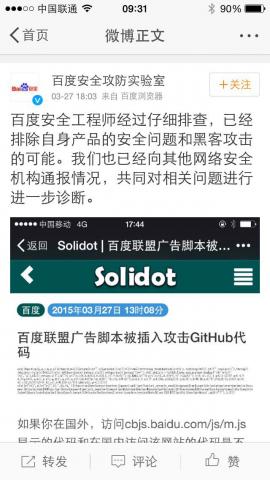
据推特消息,北京时间3月27日12时左右开始,从境外访问v.baidu.com的时候被发现会出现Javascript alert出现的弹窗:WARNING: malicious javascript detected on this domain 。追查发现是百度广告管家的jshttp://cbjs.baidu.com/js/m.js?_=1427431567741在境外访问时被替换成一段特殊的js(详细请求和返回的js)。
分析认为,大致的流程就是: 1. GFW把某些常见网站的JS替换成以上js。2. 全球各地访问国内网站时,相当于成为DDoS的源(可能还有全国各地访问国外时,未经确认)3. GitHub不堪重负,把https://github.com/greatfire/ 和https://github.com/cn-nytimes/ 的返回改成一个alert: WARNING: malicious javascript detected on this domain (网站存在恶意JS代码调用)。当境外用户访问内置境内一些网站如百度的JS调用的网站时,中国的国家防火墙GFW将这部分调用替换成重定向至目标网站,以调用民用流量的方式,实现对目标网站的DDOS攻击。GreatFire在3月中曾遭到来自中国的DDoS攻击。针对此次攻击,Greatfire正在进行调查。
技术人士@yegle 认为,用js来实现攻击远胜过早年利用DNS污染的DDOS攻击,只损失了百度的revenue,但能实现单页面反复攻击多个目标。为什么要劫持百度来攻击GITHUB呢? Larry Salibra认为:1. 这方式的优点是可以无需劫持大量电脑,也可以让网站访客在不自觉的情况下成了攻击行动的帮凶; 2. 让人产生攻击是来自中国境外的错觉 3. 希望透过服务供应商向外国媒体施压,删除中共官方不喜欢的内容。
其实不一定需要访问百度,中国国内一些论坛等网站都被植入了百度联盟广告,GFW给他们的 JS 插入了攻击代码,用户读取之后就去攻击 GitHub 了。国内用户访问百度不经过GFW,只有翻墙者会被变成攻击者。另有推特网友分析指,“一个真正的海外用户,首选搜索引擎应该是谷歌而不是百度。那么,来自海外IP对百度的访问,多数应该是通过代理翻墙的境内用户。这样GFW就可以收集很多用户的代理IP,并且通过搜索行为等判断是否翻墙。估计又会有很多VPN和翻墙软件会失效”。
翻墙者@bitinn 表示: 利用平民上网的正常流量进行DDoS已经成为中国全新的政治武器。新的被害者是:GitHub。换而言之,我们已经从Defensive(防卫)变为Offensive(攻击)了。百度攻防安全实验室官方微博28日上午否认此次攻击与自身安全性有关,称:“百度安全工程师经过仔细排查,已经排除自身产品的安全问题和黑客攻击的可能。我们也已经向其他网络安全机构通报情况,共同对相关问题进行进一步诊断”。如若属实,当可确认攻击来自GFW。
有分析认为,无论攻击脸书还是GitHub,终极目标都是逼迫对方自我审查。脸书在去年六月二十日遭受GFW发起的核弹流量攻击之后,扎克伯格桌上惊现“习近平著作”。迫使GitHub“下架”翻墙软件,是昨天攻击行为的最合理解释。与此同时,知乎上相关问题讨论的帖子已全部被删除。
有网友支招应对方法,屏蔽所有百度的JS代码:在Chrome的设置->显示高级设置->隐私设置->内容设置->JavaScript->管理例外情况中,输入百度的网址(需要通配符,如图),再将行为设置为禁用即可:Chrome://settings/contentExceptions#javascript。
文/
Sylar
(泡泡报道) IT技术人员的圣地Github正在受到该论坛史上最大的网络攻击,Github日前在其博客上公开说。各方分析显示,此次攻击来自中国,且攻击技术高超:基本上,中国的翻墙者正在无意识中被劫持加入网络攻击,成为肉鸡。Github在博客中表示,此次攻击是“为了迫使其删除一些内容”。据分析认为,此次攻击具体是针对网络自由组织GreatFire等在Github上提供的免翻墙信息服务,但影响到了整个Github。
更新(3月30日北京时间20:00):
3月30日,在中国外交部的例行记者会上,当记者问到最近的网络攻击是否来自中国时,交部发言人华春莹并未“否认”,也为对此作出正面回答,强调“中国是黑客攻击最主要的受害者之一”:
近期似乎只要是美国或者其他哪个国家有网站受到攻击,就会有人联想是不是中方黑客所为,这很奇怪。我想提醒你,中国是网络黑客攻击的最主 要的受害者之一。我们一直强调,中方希望同国际社会一道,加快制订国际规范,共同维护好网络空间的和平、安全、开放与合作。希望各方都能以积极、建设性态 度合作应对网络黑客攻击问题。
翻墙上百度,网民变黑客
据推特消息,北京时间3月27日12时左右开始,从境外访问v.baidu.com的时候被发现会出现Javascript alert出现的弹窗:WARNING: malicious javascript detected on this domain 。追查发现是百度广告管家的jshttp://cbjs.baidu.com/js/m.js?_=1427431567741在境外访问时被替换成一段特殊的js(详细请求和返回的js)。
分析认为,大致的流程就是: 1. GFW把某些常见网站的JS替换成以上js。2. 全球各地访问国内网站时,相当于成为DDoS的源(可能还有全国各地访问国外时,未经确认)3. GitHub不堪重负,把https://github.com/greatfire/ 和https://github.com/cn-nytimes/ 的返回改成一个alert: WARNING: malicious javascript detected on this domain (网站存在恶意JS代码调用)。当境外用户访问内置境内一些网站如百度的JS调用的网站时,中国的国家防火墙GFW将这部分调用替换成重定向至目标网站,以调用民用流量的方式,实现对目标网站的DDOS攻击。GreatFire在3月中曾遭到来自中国的DDoS攻击。针对此次攻击,Greatfire正在进行调查。
技术人士@yegle 认为,用js来实现攻击远胜过早年利用DNS污染的DDOS攻击,只损失了百度的revenue,但能实现单页面反复攻击多个目标。为什么要劫持百度来攻击GITHUB呢? Larry Salibra认为:1. 这方式的优点是可以无需劫持大量电脑,也可以让网站访客在不自觉的情况下成了攻击行动的帮凶; 2. 让人产生攻击是来自中国境外的错觉 3. 希望透过服务供应商向外国媒体施压,删除中共官方不喜欢的内容。
其实不一定需要访问百度,中国国内一些论坛等网站都被植入了百度联盟广告,GFW给他们的 JS 插入了攻击代码,用户读取之后就去攻击 GitHub 了。国内用户访问百度不经过GFW,只有翻墙者会被变成攻击者。另有推特网友分析指,“一个真正的海外用户,首选搜索引擎应该是谷歌而不是百度。那么,来自海外IP对百度的访问,多数应该是通过代理翻墙的境内用户。这样GFW就可以收集很多用户的代理IP,并且通过搜索行为等判断是否翻墙。估计又会有很多VPN和翻墙软件会失效”。
翻墙者@bitinn 表示: 利用平民上网的正常流量进行DDoS已经成为中国全新的政治武器。新的被害者是:GitHub。换而言之,我们已经从Defensive(防卫)变为Offensive(攻击)了。百度攻防安全实验室官方微博28日上午否认此次攻击与自身安全性有关,称:“百度安全工程师经过仔细排查,已经排除自身产品的安全问题和黑客攻击的可能。我们也已经向其他网络安全机构通报情况,共同对相关问题进行进一步诊断”。如若属实,当可确认攻击来自GFW。
有分析认为,无论攻击脸书还是GitHub,终极目标都是逼迫对方自我审查。脸书在去年六月二十日遭受GFW发起的核弹流量攻击之后,扎克伯格桌上惊现“习近平著作”。迫使GitHub“下架”翻墙软件,是昨天攻击行为的最合理解释。与此同时,知乎上相关问题讨论的帖子已全部被删除。
有网友支招应对方法,屏蔽所有百度的JS代码:在Chrome的设置->显示高级设置->隐私设置->内容设置->JavaScript->管理例外情况中,输入百度的网址(需要通配符,如图),再将行为设置为禁用即可:Chrome://settings/contentExceptions#javascript。
到截稿为止,对Github的攻击仍在持续中。3月30日,Github在推特上表示,攻击的方法已经转变,该网站在全力对抗。
中国互联网络信息中心发布中间人攻击证书
就在此前,3月25号,"中国的网络审查网站"(greatfire.org)发布声明称,从他们掌握的具体证据看,中国互联网络信息中心(CNNIC)和网信办(CAC)参与了攻击全球电子信息巨头如谷歌、微软以及火狐的行动,该证书冒充成受信任的谷歌的域名,被用于部署到网络防火墙中,用于劫持所有处于该防火墙后的HTTPS网络通信,而绕过浏览器警告。greatfire提醒有关互联网企业加强互联网防范措施,并再次呼吁谷歌、Mozilla、微软和苹果立即取消对CNNIC的信任,以保护全球网民的用户信息。
谷歌和Mozilla(火狐)分别公开了这一安全事件,就此分别发表了博客文章(Google, Mozilla)。但谷歌与Mozilla有关CNNIC发布中间人攻击证书文章的中文翻译,则在中国被勒令删除了。
23日,谷歌公司一名网络安全专家在其公司的博客专栏发表博文写道,中国互联网络信息中心以及一家被称为MCS的控股公司,为一些谷歌网址分发了没有得到授权的电子认证,"而这些被滥用的电子认证则被几乎所有的浏览器以及操作系统接受"。这名谷歌的网络安全专家将这一结果描述为互联网认证管理系统里的"软肋"。次日,微软以及火狐等公司均发表了声明,称他们将取消所有MCS发放的认证。
具有攻击性的墙
推特网友@hnjhj 表示,小组长(习近平)上台以后尽管网络管制思路跟之前一致,但路子毕竟野了很多。从3月中旬以来,CNNIC颁发官方假证书进行中间人攻击、GFW劫持全球网络流量发动DDoS攻击、强调网络主权等等的事,如果从积极方面看的话,那就是在当局看来,单纯的砌墙防御已经不够用了,翻墙途经越来越多,不主动出击就是等死。
有不少人曾传,中国的防火墙将会在今年4月完成升级。虽然目前该消息并未得到证实,细节也尚未浮出水面,但3月以来这些变化显示,墙不再是单纯的保守封锁,已沦为攻击武器,还要利用翻墙者的积极性调用民间流量,让抗争者在不知不觉中充当枪手。但翻墙者不是纯粹的无畏派,并非只有搭梯子一种技能,拒绝做肉鸡以及如何对越来越流氓的GFW发起反击是急需考虑的内容,虽然目前只能见招拆招。
时评人Larry指出:GFW从被动封锁转向主动攻击,是中共当局封锁网络“有害信息”、确保政治安全的需要的扩大化,与中国网络用户越来越强烈的“自由、开放、安全”的网络需求之间不可调和的矛盾冲突的表现。极权势力投入在网络控制的资源不断扩张,对应的就是反对网络控制、追求言论通信自由的呼声越来越强烈。
【英文版文章如下】
Chinese netizens weaponized, resulted in the “largest DDoS attack” in GitHub’s history
GitHub, a website where technicians and coders around the world share experience, has been busy for the past four days mitigating the “largest DDoS attack” in its history. China has been cited as Wall the source of the attack. Perhaps a more frightening fact is that, internet users in China have been turned into attackers during this cyber-attack, without their knowledge.
The targets are GreatFire’s anti-censorship programs and New Yorks Time China on Github, according to an analysis report from Netresec.
At a press conference on March 30th, Chinese Foreign Ministry did not confirm or deny if Chinese government is behind this attack. Hua Chunying, the spokeswoman of the ministry said:
Some people associate Chinese hackers with recent cyber-attacks on websites in US or elsewhere, this is very strange. I would like to remind you that, China is one of the biggest victims of cyber-attacks. We have always stressed that, China hopes to work together with the international society… to uphold a peaceful, secure, open and cooperative cyber environment.
Turn Netizens into Hackers
Starting from March 27, 12 PM (Beijing Time), when people visit Chinese websites using VPNs to bypass Chinese censorship, it was very likely that they were turned into attackers by a malicious code embedded in the Baidu ads. Instantly, their computers will be recruited to join the attack at GitHub.
Baidu is like China’s Google and many Chinese websites using tracking and advertising code from Baidu. The attack has been dubbed as “HTTP hijacking”: “a certain device at the border of China’s inner network and the Internet has hijacked the HTTP connections” and “replaced some JavaScript files from Baidu with malicious ones” that would load GitHub’s GreatFire and CN-NYTimes projects “every two seconds.”
This will influence internet users who visit Chinese websites via an IP address outside China, including Chinese users who use VPNs or other circumvention tools. In its official weibo account, Baidu Security Lab denied that the attack was related to their security loopholes.
“using regular internet users to engage in DDoS attack is now China’s new political weapon. “User @bitinn wrote, “(Chinese censors) has switched from simply defense to active offense.”
From Defense to Offense
Indeed, recently Chinese internet censorship mechanism has become more aggressive, and actively attack sites that are deemed too sensitive by the censors. Since this March, China has been accused of DDoS attack Greatfire’s anti-censorship mirror sites. Last week, Google found unauthorized digital certificates for several Google domains, the root CA of which is Chinese Internet network information center (CNNIC). Google and Mozilla both publicly disclosed this security incident and published blog posts(Google,Mozilla).Chinese Internet network information center.
Github stated in its blog that, the intent of this attack is “to convince us to remove a specific class of content. “ Before this article is published, GitHub is still working to mitigate the attack.
中国互联网络信息中心发布中间人攻击证书
就在此前,3月25号,"中国的网络审查网站"(greatfire.org)发布声明称,从他们掌握的具体证据看,中国互联网络信息中心(CNNIC)和网信办(CAC)参与了攻击全球电子信息巨头如谷歌、微软以及火狐的行动,该证书冒充成受信任的谷歌的域名,被用于部署到网络防火墙中,用于劫持所有处于该防火墙后的HTTPS网络通信,而绕过浏览器警告。greatfire提醒有关互联网企业加强互联网防范措施,并再次呼吁谷歌、Mozilla、微软和苹果立即取消对CNNIC的信任,以保护全球网民的用户信息。
谷歌和Mozilla(火狐)分别公开了这一安全事件,就此分别发表了博客文章(Google, Mozilla)。但谷歌与Mozilla有关CNNIC发布中间人攻击证书文章的中文翻译,则在中国被勒令删除了。
23日,谷歌公司一名网络安全专家在其公司的博客专栏发表博文写道,中国互联网络信息中心以及一家被称为MCS的控股公司,为一些谷歌网址分发了没有得到授权的电子认证,"而这些被滥用的电子认证则被几乎所有的浏览器以及操作系统接受"。这名谷歌的网络安全专家将这一结果描述为互联网认证管理系统里的"软肋"。次日,微软以及火狐等公司均发表了声明,称他们将取消所有MCS发放的认证。
具有攻击性的墙
推特网友@hnjhj 表示,小组长(习近平)上台以后尽管网络管制思路跟之前一致,但路子毕竟野了很多。从3月中旬以来,CNNIC颁发官方假证书进行中间人攻击、GFW劫持全球网络流量发动DDoS攻击、强调网络主权等等的事,如果从积极方面看的话,那就是在当局看来,单纯的砌墙防御已经不够用了,翻墙途经越来越多,不主动出击就是等死。
有不少人曾传,中国的防火墙将会在今年4月完成升级。虽然目前该消息并未得到证实,细节也尚未浮出水面,但3月以来这些变化显示,墙不再是单纯的保守封锁,已沦为攻击武器,还要利用翻墙者的积极性调用民间流量,让抗争者在不知不觉中充当枪手。但翻墙者不是纯粹的无畏派,并非只有搭梯子一种技能,拒绝做肉鸡以及如何对越来越流氓的GFW发起反击是急需考虑的内容,虽然目前只能见招拆招。
时评人Larry指出:GFW从被动封锁转向主动攻击,是中共当局封锁网络“有害信息”、确保政治安全的需要的扩大化,与中国网络用户越来越强烈的“自由、开放、安全”的网络需求之间不可调和的矛盾冲突的表现。极权势力投入在网络控制的资源不断扩张,对应的就是反对网络控制、追求言论通信自由的呼声越来越强烈。
【英文版文章如下】
Chinese netizens weaponized, resulted in the “largest DDoS attack” in GitHub’s history
GitHub, a website where technicians and coders around the world share experience, has been busy for the past four days mitigating the “largest DDoS attack” in its history. China has been cited as Wall the source of the attack. Perhaps a more frightening fact is that, internet users in China have been turned into attackers during this cyber-attack, without their knowledge.
The targets are GreatFire’s anti-censorship programs and New Yorks Time China on Github, according to an analysis report from Netresec.
At a press conference on March 30th, Chinese Foreign Ministry did not confirm or deny if Chinese government is behind this attack. Hua Chunying, the spokeswoman of the ministry said:
Some people associate Chinese hackers with recent cyber-attacks on websites in US or elsewhere, this is very strange. I would like to remind you that, China is one of the biggest victims of cyber-attacks. We have always stressed that, China hopes to work together with the international society… to uphold a peaceful, secure, open and cooperative cyber environment.
Turn Netizens into Hackers
Starting from March 27, 12 PM (Beijing Time), when people visit Chinese websites using VPNs to bypass Chinese censorship, it was very likely that they were turned into attackers by a malicious code embedded in the Baidu ads. Instantly, their computers will be recruited to join the attack at GitHub.
Baidu is like China’s Google and many Chinese websites using tracking and advertising code from Baidu. The attack has been dubbed as “HTTP hijacking”: “a certain device at the border of China’s inner network and the Internet has hijacked the HTTP connections” and “replaced some JavaScript files from Baidu with malicious ones” that would load GitHub’s GreatFire and CN-NYTimes projects “every two seconds.”
This will influence internet users who visit Chinese websites via an IP address outside China, including Chinese users who use VPNs or other circumvention tools. In its official weibo account, Baidu Security Lab denied that the attack was related to their security loopholes.
“using regular internet users to engage in DDoS attack is now China’s new political weapon. “User @bitinn wrote, “(Chinese censors) has switched from simply defense to active offense.”
From Defense to Offense
Indeed, recently Chinese internet censorship mechanism has become more aggressive, and actively attack sites that are deemed too sensitive by the censors. Since this March, China has been accused of DDoS attack Greatfire’s anti-censorship mirror sites. Last week, Google found unauthorized digital certificates for several Google domains, the root CA of which is Chinese Internet network information center (CNNIC). Google and Mozilla both publicly disclosed this security incident and published blog posts(Google,Mozilla).Chinese Internet network information center.
Github stated in its blog that, the intent of this attack is “to convince us to remove a specific class of content. “ Before this article is published, GitHub is still working to mitigate the attack.
Similar threads
家园推荐黄页
家园币系统数据
- 家园币池子报价
- 0.0097加元
- 家园币最新成交价
- 0.0101加元
- 家园币总发行量
- 1101666.53家园币
- 加元现金总量
- 12044.05加元
- 家园币总成交量
- 4098206.67家园币
- 家园币总成交价值
- 384692.02加元
- 池子家园币总量
- 396336.11家园币
- 池子加元现金总量
- 3850.24加元
- 池子币总量
- 35214.19
- 1池子币现价
- 0.2187加元
- 池子家园币总手续费
- 5731.58JYB
- 池子加元总手续费
- 595.28加元
- 入池家园币年化收益率
- 0.45%
- 入池加元年化收益率
- 4.82%
- 微比特币最新报价
- 0.086795加元
- 毫以太币最新报价
- 4.28954加元
- 微比特币总量
- 0.354108BTC
- 毫以太币总量
- 0.219250ETH
- 家园币储备总净值
- 361,566.96加元
- 家园币比特币储备
- 3.4200BTC
- 家园币以太币储备
- 15.1ETH
- 比特币的加元报价
- 86,795.20加元
- 以太币的加元报价
- 4,289.54加元
- USDT的加元报价
- 1.36805加元
- 交易币种/月度交易量
- 手续费
- 家园币
- 0.1%(0.01%-1%)
- 加元交易对(比特币等)
- 1%-2%
- USDT交易对(比特币等)
- 0.1%-0.6%




